Sovereign & Air-Gapped
Fully on-premise deployment, zero cloud dependency. Designed for classified environments.
AI-powered secure WMS for defense, government and critical infrastructure — sovereign deployment, full audit, and chain-of-custody for every critical asset.

An AI-powered, on-prem-first warehouse management platform engineered for armed forces, defense ministries, federal authorities and critical-infrastructure operators — with item-level RFID, RTLS, tamper detection and full chain-of-custody from receipt to deployment.
Fully on-premise deployment, zero cloud dependency. Designed for classified environments.
Item-level history for every weapon, round and serialized asset, end-to-end.
Native integration with command-and-control, CCTV (RAQEEB), VMS and access control.

Every rifle, sidearm, magazine and round is RFID-tagged and registered in the armory ledger. Issue, return, transfer and reconciliation are workflow-driven with multi-level approval and biometric sign-off.
Defense-grade warehouse intelligence with on-prem AI and air-gap support.
Item-level RFID for weapons, ammunition and serialized assets — full chain-of-custody.
Real-time visibility on classified hardware with restricted-zone enforcement.
Issue, return, audit and reconciliation workflows with multi-level approval.
Live tracking of soldiers, vehicles and tactical assets across base perimeters.
Workflow-driven authorisation for storage and movement of sensitive items.
Open integration with C2 systems, surveillance and incident-response platforms.
Define and enforce no-go and high-security zones with instant alerts.
Tamper detection on tags, gates and sensitive containers with active alarms.
Fully on-prem and air-gapped operation — no cloud dependency required.
Designed for UAE Armed Forces, MoD and federal-government security standards.
2D / 3D facility twin with live asset, personnel and infrastructure state.
End-to-end encryption, SAIF cybersecurity controls and hardened endpoints.
Automatic alerts, escalation paths and integration with emergency systems.
Native integration with CCTV (RAQEEB), VMS and access-control systems.
Full audit trail and forensic-grade history for every critical asset.
Role and clearance-based access — from soldier to senior commander.
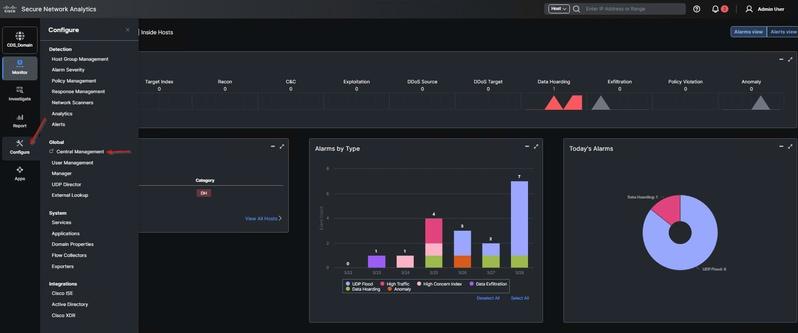
Live dashboards aggregate inventory state, RFID events, RTLS positions, gate alerts and surveillance feeds into a single command interface — ready to plug into existing C2 stacks via secure APIs.






On-prem deployment for a single armory or base — rapid install, fully air-gapped.
Federated deployment across multiple bases with regional roll-up command view.
National-scale deployment integrated with MoD command, surveillance and emergency systems.
From a single armory to a national defense logistics network — one platform, one chain of custody, total visibility.